Apple’s iCloud Keychain is a powerful tool that simplifies how you manage your saved passwords and sensitive information across all your Apple devices. iCloud Keychain remembers your various credentials, making it unnecessary for you to recall every single one. With the introduction of iOS 17 and macOS Sonoma, managing these saved passwords has become even more seamless with the feature of shared password groups, enabling you to share access safely with trusted individuals.
Whether you cannot approve a new device or want to ensure that your card information is stored locally on your device, iCloud Keychain has you covered. It securely syncs your data across iCloud servers, keeping your information updated and easily accessible. If you ever turn off iCloud Keychain, rest assured, knowing that an encrypted copy of your keychain data stays unique to your device and is combined with your device passcode to ensure maximum security.
Getting Started with iCloud Keychain
Embarking on the journey with iCloud Keychain begins with activation on your Apple devices. The service is designed to keep your credentials continuously synchronized across devices and shared with your chosen people. iCloud Keychain protects your sensitive information by storing it on iCloud servers, and should you decide to disable the feature, your data remains stored locally on your device. Additionally, new shared password groups in iOS 17 and macOS Sonoma make sharing credentials with family and friends easy and secure.
Activating iCloud Keychain on iOS Devices
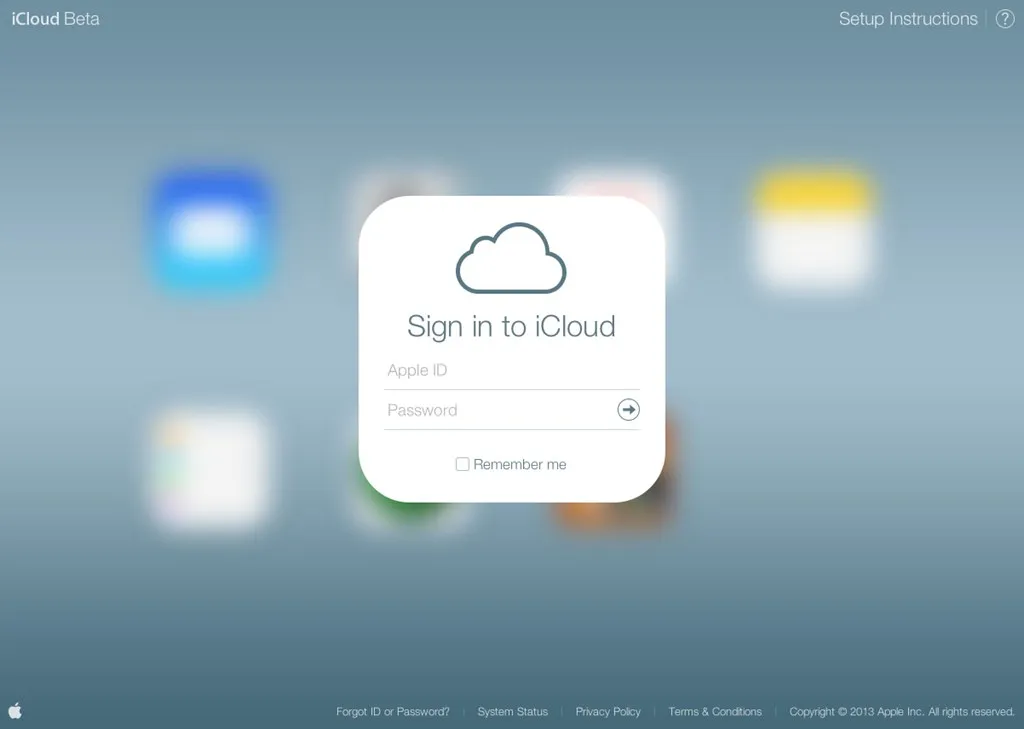
To activate iCloud Keychain on your iOS device, navigate to Settings and enter your Apple ID section. Follow the prompts to enable iCloud Keychain, which may require you to input your iCloud security code if you’re setting up a new device without access to one that is already approved. Once enabled, your saved passwords and other secure information will automatically update across your Apple devices.
Enabling iCloud Keychain on macOS
For macOS users, enabling iCloud Keychain is just as straightforward. Open System Preferences and click on your Apple ID. From there, check the box for iCloud Keychain to start syncing your saved passwords. If you decide to turn off this feature, know that your data, including passwords and card information, will be stored locally on your device, ensuring that you always have control over your personal information.
Managing Your Credentials Effortlessly
Once iCloud Keychain is up and running, managing your credentials becomes a breeze. With a dedicated passwords tab in Safari’s Preferences, you can easily view and manage your saved passwords for websites. Should you ever need to delete a password, the process is just a click away. This centralized approach ensures that your sensitive data is always at your fingertips yet securely stored and managed under Apple’s robust security protocols.
Autofill Your Credentials and Payments Seamlessly
The convenience of iCloud Keychain extends to the ability to autofill passwords and payment information. When you visit a password field in Safari or other compatible apps on your iPhone or iPad, select iCloud Keychain, and an Apple ID prompt will appear. The iCloud Keychain autofill function streamlines the process, so you don’t have to remember each individual login. On your Mac, you can activate this feature within the Safari browser via the Autofill tab in Safari Preferences.
Autocompleting Passwords in Safari
Navigating the web becomes more secure and efficient with iCloud Keychain’s ability to autocomplete passwords in Safari. The passwords tab within Safari’s Preferences stores your login credentials and helps protect against data breaches by alerting you to compromised passwords. To further enhance security, you can set up 2FA for accounts and securely store card numbers for quick and easy payments.
Manually Adding New Logins to Your Vault
Even without the prompts of a website, iCloud Keychain allows you to store your logins and passwords proactively. On your iOS device, simply navigate to the passwords tab within the Settings and tap the ’+’ symbol to add your credentials. Input your username and password for any website of your choice. For Mac users, the process is just as straightforward. Open Safari, go to Preferences and select Passwords. Click the ‘Add’ button to create a new password profile with the website’s URL, username, and password, akin to a third-party password manager.
Enhancing Security and Accessibility
Apple’s iCloud Keychain is fortified with industry-standard encryption techniques, ensuring your sensitive data stays secure. You can keep your information solely on your device; simply skip the Apple security code during setup. However, it’s worth noting that this choice precludes Apple’s ability to recover your keychain data should it be lost, as your keychain information will not be backed up to the cloud.
Leveraging Face ID and Touch ID for Quick Access
Maximizing the potential of iCloud Keychain involves using Apple’s biometric systems for expedient password filling. Activate Face ID or Touch ID, depending on your device—Face ID & Passcode on iPhone, Touch ID & Passcode on the new iPad Air, or the Touch ID preference on your Mac. This integration eliminates the need to repeatedly enter your Apple ID password or passcode, streamlining the process of auto-filling credentials on your Apple devices.
Safeguarding Notes with Secure Encryption
For iOS devices, iCloud Keychain provides more than just password management; it pairs with the Keychain Access app on Mac to bolster security. This powerful tool allows you to view system keys and create secure notes only accessible with your Mac password. Similar to securing a note in the Notes app, this feature ensures that the information you need to remember stays protected and private, separate from your stored login credentials.

Troubleshooting and Optimization Tips
If iCloud Keychain is unexpectedly disabled, your passwords and other secure information remain on your device, but updates and shared access will cease. In such cases, verify your settings and reconnect to iCloud Keychain to continue synchronizing your data across devices and with trusted individuals. Should you sign out of iCloud while Keychain is active, be aware that changes made will not be reflected on your device.
What to Do If iCloud Keychain Is Turned Off Unexpectedly
When iCloud Keychain deactivates without your intervention, ensure your device settings have not been altered. You can reset your end-to-end encrypted data following the on-screen prompts if needed. Remember, if you disable iCloud Keychain, your information will be stored locally, and any modifications will not sync across your devices or with trusted contacts.
Checking and Updating Compromised Passwords
Stay vigilant against security breaches by regularly reviewing your passwords within the iCloud Keychain. iOS and macOS provide tools to identify and update compromised passwords, ensuring your digital presence remains secure. As a proactive measure, share passwords and passkeys with people you trust, using the shared password groups feature available on the latest versions of iOS and macOS.
Expanding Your Password Management Toolkit
While iCloud Keychain excels within the Apple ecosystem, integrating it with other platforms can enhance its utility. For instance, you can bring iCloud Keychain to a Windows PC by installing iCloud for Windows and the iCloud Passwords Chrome extension. This setup allows you to access your saved passwords using Chrome, providing a seamless browsing experience akin to Safari on a Mac.
Integrating iCloud Keychain with Chrome on a Windows PC
To access your iCloud Keychain passwords on a Windows PC, download and update iCloud for Windows. Next, add the iCloud Passwords extension from the Chrome store and sign in to activate the feature. Once verified, you can use your iCloud Keychain credentials within Chrome, bridging the gap between your Apple devices and PC browsing.
Considering a Secondary Password Manager for Additional Safety
While iCloud Keychain is a robust password manager for Apple devices, it’s not without limitations, particularly when venturing outside of iOS and macOS or sharing credentials with non-Apple browsers. In these scenarios, employing a third-party password manager can provide additional flexibility and safety, ensuring your passwords remain accessible across diverse platforms and devices.
In-Depth Understanding of iCloud Keychain
Understanding the mechanics behind iCloud Keychain’s security is crucial. Your data is protected by end-to-end encryption, which is considered the highest standard in data security. This encryption utilizes a unique key derived from your device, coupled with your device passcode—known only to you—to safeguard your information during transmission and stored.
How iCloud Keychain Maintains the Privacy of Your Information
iCloud Keychain’s privacy assurance is anchored in end-to-end encryption, ensuring your data is always protected. The encryption key, generated from your device-specific information and bolstered by your device passcode, is known solely to you. This robust security measure guarantees that your data remains inaccessible to unauthorized parties, whether in transit or at rest.
Mastering Passwords with iCloud Keychain: Strategies for Proactive Protection
Safeguard your digital identity with iCloud Keychain and two-factor authentication for Apple ID. Enable this crucial security layer to prevent unauthorized access. Ensure seamless syncing across devices by updating to the latest macOS or iOS. Regularly review stored passwords in Safari’s Autofill or iCloud Keychain to prevent data leaks. Gain quick, secure access with Safari’s autofill feature. Approve only trusted devices to protect sensitive information like Wi-Fi passwords and credit card details.
