As digital threats continue to evolve, understanding the distinction between anti-virus and anti-malware tools is crucial for effective digital protection. While software scans are integral to both, knowing their capabilities and limitations forms the bedrock of cybersecurity strategy. By staying informed and updating your security solutions, you guard against the latest cyber threats, ensuring robust defense for your digital assets.
Adopting a comprehensive approach to security means recognizing that no single solution is infallible. When your software scans for threats, it’s imperative to ensure that updates are regularly applied. This enables your anti-malware to identify and thwart the newest attacks, fortifying your defenses against an ever-changing threat landscape.

Understanding the Fundamentals
To effectively navigate the terrain of cyber defense, it’s essential to grasp the basic concepts underlying viruses and malware. These digital nuisances range from disruptive to destructive, with each variant exhibiting unique behaviors and threats. A foundational understanding of these terms equips you with the knowledge to select and manage the appropriate protective measures for your system.
Defining Malware and Its Variants
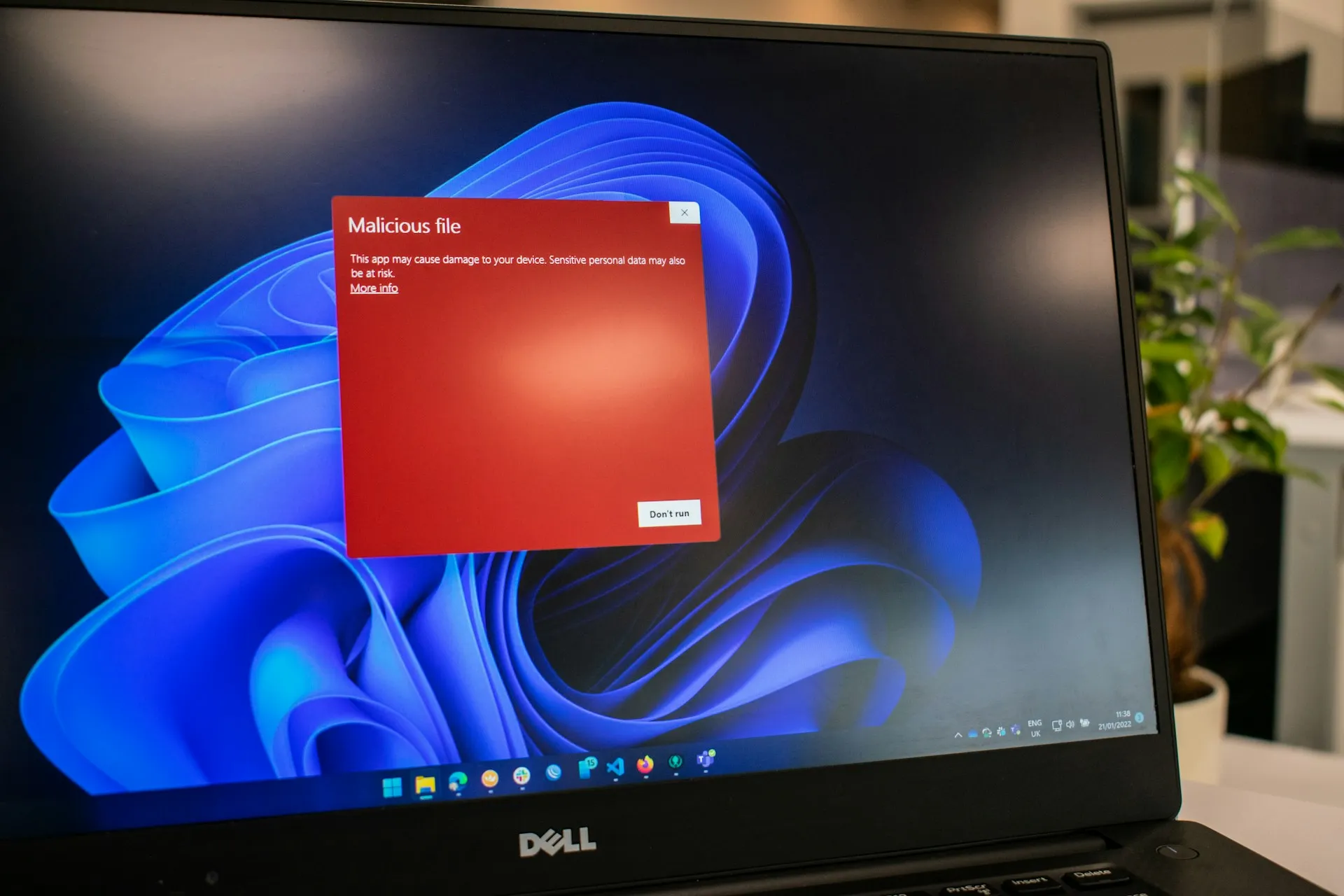
Malware, the umbrella term for a variety of malicious software, encompasses viruses, Trojans, spyware, worms, adware, ransomware, and more. Each type is designed with a purpose, whether it’s to gain unauthorized access, corrupt your system or destroy data, posing distinct challenges to users and their digital environments. Recognizing these variants is the first step in crafting an effective defense strategy.
Breaking Down What Constitutes a Virus
Viruses are a specific type of malware that replicates by attaching to files or programs with the intent of causing damage to your computer. They can spread uncontrollably, corrupting systems or destroying data. Though considered legacy threats, viruses highlight the need for vigilance and the importance of employing security solutions adept at managing traditional virus and malware threats.
Diving Into Anti-Virus Solutions
Exploring anti-virus solutions is pivotal in safeguarding against the threats that target our digital ecosystems. These solutions serve as the first line of defense, designed to detect, prevent, and eliminate viruses, thereby mitigating the risk of malware infection and ensuring the integrity of our computer systems.
Key Features of Effective Anti-Virus Software
Effective anti-virus programs offer ransomware protection, proactive security measures, and the capability to remove malware from an infected computer. They include software scans to test suspected threats, blocking access to suspicious servers, and tools for systematically removing malware, safeguarding against potential malware and its distribution.
Pros of Utilizing Anti-Virus Protection
One of the foremost benefits of anti-virus protection is its ability to perform comprehensive software scans, which are instrumental in detecting and neutralizing known threats. This proactive scanning mechanism is crucial for maintaining system integrity and preventing malware infection.
Cons of Solely Relying on Anti-Virus
However, relying solely on anti-virus software can be shortsighted. While it’s effective against known threats, it may not be as adept at identifying and mitigating newly emerged or sophisticated cyber threats, which are constantly evolving and require more advanced detection methods. To bolster your security, using a super strong password generator online is crucial. This tool helps you create strong, complex passwords that are difficult for hackers to crack, adding an extra layer of protection to your accounts.

Exploring Anti-Malware Mechanisms
Anti-malware programs extend beyond the traditional antivirus capabilities, offering enhanced protection against a broader spectrum of cyber threats. They are designed to adapt to the constantly evolving malware landscape, ensuring that known and emerging threats are effectively countered.
Core Functions of Anti-Malware Programs
The core functions of anti-malware programs revolve around detecting and neutralizing cyber threats that traditional antivirus may overlook. These sophisticated tools adapt to the constantly evolving nature of malware, providing an additional layer of security to combat advanced and emerging threats.
Pros of Implementing Anti-Malware Measures
Implementing anti-malware measures provides a robust defense against sophisticated cyber threats that might evade traditional antivirus solutions. These advanced tools excel in identifying and mitigating a wide array of malware types, enhancing your system’s security posture. A specialized tool for checking your email for breaches can further help in detecting unauthorized access and preventing future incidents. By using this tool, you can quickly identify suspicious activities and ensure your email communications remain secure.
Cons of Anti-Malware as a Standalone Solution
Relying on anti-malware alone, however, might leave gaps in your security strategy. Some anti-malware solutions might not cover all aspects of virus protection, potentially leaving your system vulnerable to specific attacks requiring specialized antivirus defenses.
The Comparative Analysis: Anti-Virus vs Anti-Malware
Comparing anti-virus to anti-malware tools reveals distinct functionalities and areas of expertise. Understanding the differences between these tools is essential in determining the appropriate product for your specific needs, ensuring maximum protection for your digital environment.
The Distinct Roles of Anti-Virus and Anti-Malware Tools
While anti-virus software is tailored towards preventing and eliminating traditional viruses, anti-malware tools are designed to offer a broader security net against a range of malicious software. Each serves a distinct role in the cybersecurity ecosystem, addressing different aspects of digital protection.
The Synergy of Dual Protection Strategies
Employing both antivirus and anti-malware software can create a synergistic effect, enhancing the overall security of your digital environment. This dual strategy ensures comprehensive coverage, safeguarding against different types of malware, including viruses, worms, Trojans, spyware, adware, and ransomware.
Selecting the Right Software for Your Needs
Choosing the optimal security software requires an understanding that cyber threats are constantly evolving, making it essential that your digital defense can adapt. Traditional antivirus may fail to detect every type of infection, particularly with sophisticated malware. Therefore, it’s crucial to assess the capabilities of both antivirus and antimalware programs to ensure comprehensive protection.
Criteria for Picking Quality Anti-Virus Software
When selecting anti-virus software, prioritize a solution that can effectively scan for viruses and combat various forms of malicious software. Look for features such as real-time protection, frequent updates to tackle new malware threats, and a user-friendly interface. Seamlessly integrating into your system without compromising performance is also a key consideration.
Determining the Best Anti-Malware Solution
The best anti-malware solution offers robust protection against new malware, including zero-day attacks and ransomware. It should detect and remove dangerous malware promptly while maintaining a database of known malware to prevent future infiltrations. Consider factors like system impact, ease of use, and whether the software provides real-time protection.
Price Considerations in Security Software Selection
The cost of security software varies, but expensive doesn’t always mean better. Budget-friendly options can provide substantial protection without the high price tag. It’s important to evaluate the features offered in relation to the cost and determine if the software meets your specific security needs without overextending your budget.
Free versions of antivirus and antimalware can be enticing, yet they often come with limitations. Assess whether these restrictions align with your security expectations or if investing in a paid version is necessary for comprehensive coverage. Remember, achieving the best balance between cost and cybersecurity effectiveness is the goal.
Consider the long-term financial implications of your choice, including subscription fees or costs associated with upgrades. Some programs offer a one-time purchase, while others operate on a subscription model. Evaluate which pricing structure suits your financial planning and offers the required flexibility.
Lastly, consider bundled offerings or deals that may include additional security features or services. These packages can provide greater value, combining antivirus, anti-malware, and other protective measures at a more affordable rate than purchasing them separately.
Top Questions Answered
Regarding the effectiveness of anti-virus versus anti-malware, each serves a distinct purpose. Anti-virus protects users from the latest computer viruses and other known online threats, while anti-malware shields against a broader range of malicious programs, including dangerous threats like polymorphic malware, ransomware attacks, and phishing attempts.
Effectiveness of Anti-Virus vs Anti-Malware
Anti-virus software is adept at providing a fundamental layer of defense against established threats, employing a database of known malware for detection. On the other hand, anti-malware casts a wider net, protecting against various kinds of malware, from Trojan horses to unwanted spyware programs, and often updates its rules faster than antivirus software to respond to emerging cyber-attacks.
The Possibility of Running Concurrent Security Programs
While running concurrent security programs is possible, doing so can lead to system conflicts and reduced performance. It’s typically advised to use a comprehensive solution that combines antivirus and antimalware capabilities or to carefully select compatible programs that complement each other without overlapping functionality.
Safeguarding Your Digital Environment with These Tools
For advanced cybersecurity needs, the tools we shared provide a range of software designed to protect endpoints from cybersecurity threats. For instance, their Endpoint Detection and Response (EDR) system goes beyond traditional defenses, offering proactive monitoring and rapid response to suspicious activities, ensuring a fortified digital environment.
Bitdefender
One of the stalwarts in this domain is Bitdefender. Renowned for its advanced threat detection capabilities, Bitdefender employs a multi-layered approach to identify and neutralize viruses, ransomware, and other malware. Its real-time scanning and behavioral analysis ensure proactive defense, earning it accolades as one of the top choices in cybersecurity.
Kaspersky
Kaspersky Anti-Virus stands out for its exceptional malware detection rates and efficient resource utilization. With features like real-time protection, heuristic analysis, and a powerful firewall, Kaspersky provides a formidable defense against evolving cyber threats. Its continuous updates ensure users are shielded from the latest malware strains.
Malwarebytes
For those seeking a user-friendly yet robust solution, Malwarebytes proves to be a formidable contender. Malwarebytes specializes in malware removal and employs signature-based and behavior-based detection to identify and eliminate threats. It is particularly effective in combating adware and spyware, making it a popular choice for users prioritizing simplicity without compromising security.
Sophos Endpoint Protection
Sophos Endpoint Protection offers enterprise-grade security with a focus on simplicity. With features like web filtering, device control, and advanced threat protection, Sophos ensures comprehensive defense against various cyber threats. Its centralized management console simplifies administration for organizations of varying sizes.
While these tools excel in various aspects, it’s crucial to emphasize the importance of regular updates, user education, and cautious online behavior. No antivirus or anti-malware tool can provide absolute immunity, and a holistic approach to cybersecurity remains the key to a resilient defense against the ever-evolving landscape of digital threats.
Deciphering Your Digital Defense Strategy
Choosing the right protection for your devices boils down to understanding the unique threats they face and the appropriate defensive tools available. Anti-virus software offers a fundamental shield against traditional viruses, while anti-malware programs, such as Malwarebytes Premium, provide a more comprehensive online security solution against various threats, including ransomware, spyware, and phishing attacks. Ultimately, a layered defense strategy employing both types of protection will most effectively secure your digital world from the ever-evolving landscape of cyber threats.
