Strong Password Checker: Measure Your Password Strength
Is your password strong enough to withstand cracking attempts? Verify its strength with our password tester tool and learn how to create secure passwords to stay protected online.
How to Create a Secure Password
Constructing truly secure passwords blocks most criminals and hackers in their tracks. The core components for fortress-like password protection include complexity, uniqueness, length, and proper storage.
Complex Characters
All strong passwords leverage length as well as a mixture of different character types - uppercase & lowercase letters, numbers, and symbols. Incorporating character variety introduces password entropy, which exponentially expands the possible password combinations a criminal would need to test.
When codes contain only one character type, like all lowercase letters, a 7-character password yields 26^7 or 8,031,810,176 possible combinations. Adding capital letters expands combinations to 52^7 equals 35,217,908,176. Mixing in numbers 0-9 significantly jumps to 62 potential characters per slot or 218,340,105,584,896 combinations! Finally, blending in special symbols allows 94 possible characters per position and 5.7 undecillion total combinations.
Maximizing character diversity directly strengthens password complexity. Special symbols especially frustrate brute forcing attempts and dictionary attacks that expect passwords drawn solely from alphabetical keyboards.
Passphrases
Human-readable passphrases enable excellent security through extreme length rather than complexity. Think of a short, quirky sentence like “BigM0uthBaSsSwim2Lake55”. At over 20 characters, the length creates sufficient password entropy to withstand most attacks despite the lack of special characters. This technique aids memorability without sacrificing strength since the sentence structure provides a cue.
For maximum safety, combine the passphrase and complexity tactics. Construct a lengthy, memorable sentence with added symbols, numbers, and mixed case like “J@ck&J1llRanUpTh3H!ll32”. Going beyond 20 characters covers all bases.
Randomness
Truly random password generation currently remains impossible for humans to achieve manually. We inevitably lean on patterns, phrases, names, dates, keyboard rows, or other non-random influences.
For guaranteed strong credentials without the memory burden, use our secure random password generator tools. Random password managers create long codes with all the character types mixed unpredictably. It fully thwarts brute forcing due to the complete randomness.
To maximize safety, avoid common words, repeated characters (aaa), incremental sequences (123), adjacent keyboard keys (qwerty), and personal information. Prioritize fully random characters for strong passwords.
Why Use Password Strength Checker?
Our password tester or strength testing tool analyzes the construction of passwords to benchmark their resilience against common attacks like brute forcing.
Password checkers evaluate metrics like:
- Length - longer is stronger by expanding possible combinations
- Character types used - more randomness improves strength
- Character diversity within types - using more of the potential letters, numbers, and symbols increases combinations
- Sequence patterns - consecutive characters or repeated strings weaken passwords by improving the odds of guessing
The password analysis method calculates a numeric score for overall password quality and generate a strength rating from predefined grading levels (very weak, weak, good, strong and very strong).
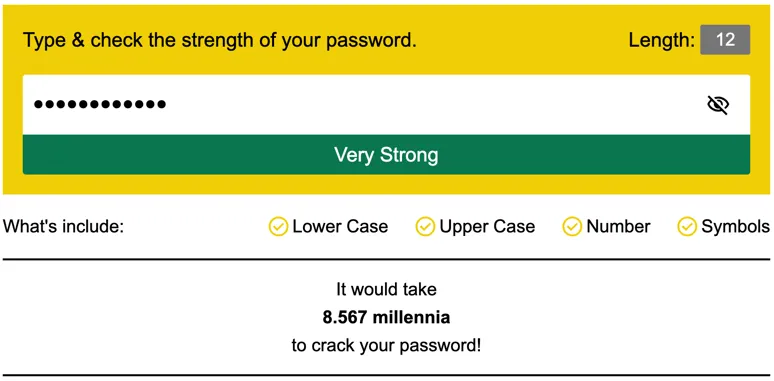
How do password strength testers work exactly? Password strength checker feed the password string into testing suites designed around known password cracking principles and data breach pattern analysis.
The checker runs check like:
- Calculating total password variations based on length and character types
- Scanning for sequences, repeats, and other easily guessable patterns
These tests determine how quickly the password would succumb to common attacks by calculating the guesses and time required to randomly crack the password’s maximum variations. More combinations and randomness equals a stronger rating. Weak, predictable patterns drastically reduce variation combinations and get lower scores.
Why Strong Passwords Matter
Passwords are the keys to our digital lives - they protect access to our most sensitive information and accounts. We entrust vital data like financial records, personal communications, photos, and more to various online services. Strong passwords act as the frontline defense to ensure only we can access our private information.
With data breaches exposing over 37 billion records in 2021 alone, having secure login credentials is crucial. Cybercriminals use compromised passwords in brute force attacks to gain access to other accounts since people tend to reuse passwords across multiple sites. Strong, unique passwords for every service prevent criminals from exploiting this dangerous password reuse.
When learning password best practices and testing password strength, we proactively enhance our cybersecurity posture. Password creation strategies, proper password storage, and when to change passwords empower us to lock down our digital assets. Applying password guidelines allows us to maximize password security and minimize vulnerabilities.
The Risks of Weak Passwords
Weak passwords seriously jeopardize our privacy and security. They make us prime targets for brute force attacks, which automatically guess credentials using common phrases and patterns. Poorly constructed passwords are easily discovered through these attacks or even simple guessing based on details like names, birthdays, and dictionary words.
Once hackers gain access to one account protected by a weak password, data like usernames, security questions, and email addresses unlock more account access. By exploiting password reuse, hackers often trigger a domino effect where one compromised password leads to many breached accounts. It enables massive digital theft, financial fraud, and personal violations. You can also check if your email address has been compromised with our email hack checker.
Weak passwords also contribute to damaging data breaches. When employers, online services, and device makers fail to implement adequate password policies and encryption, customer data is left vulnerable. Weak passwords only compound this issue and directly aid hackers in accessing sensitive systems to steal confidential information.
Best Practices for Password Security
Combining strong, unique passwords across accounts with secure password management establishes robust protection for our digital lives.
Make Passwords Unique and Unpredictable
Password uniqueness prevents chain reactions if one account suffers a breach. Cybercriminals exploit password reuse across accounts, so distinct passwords for every service block this tactic.
Unpredictable passwords also thwart data leaks, social engineering, and brute force attacks. Info like names, dates, pet names, addresses, phone numbers, keyboard patterns, and dictionary words all seem like convenient password choices but offer no protection. Prioritize fully random strings.
Optimize Password Length for Security
Length directly fuels password strength. At 10-12 randomly generated characters, brute forcing becomes arduous. The above 16 characters offer excellent protection fitting over 128-bit encryption. The longest randomly generated password your memory can comfortably retain makes the best choice — 20+ characters as a passphrase or managed password provides an ideal defense.
Use a Secure Password Manager
Password managers allow users to have distinct, complex, lengthy passwords for every account while only needing to remember one master credential. These password vault apps offer:
- Secure encrypted storage of login credentials offline
- Password generation with full customization options
- Multi-factor authentication for accessing the vault
- Password autofill to alleviate memorization
- Password sharing securely between approved users
- Cross-platform accessibility
Leading password managers like Dashlane, LastPass, and 1Password help consumers implement robust password policies with far less effort.
When delegating credential storage to encrypted managers, we gain simplicity without sacrificing security. The combination of complex, unique passwords and password managers exemplifies defense in depth for user access management.
Frequently Asked Questions
Is it safe to use a password strength checker?
Reputable online password checkers from leading cybersecurity tools use best practices to analyze rather than store or collect passwords. They process the password data algorithmically on your device and then discard it rather than transmitting or saving passwords externally. It allows safe checking to strengthen credentials. However, avoid entering passwords on unfamiliar or questionable sites.
How long would it take a computer to crack my password?
The time depends primarily on password length & complexity. An 8-character password using only lowercase letters takes ~2 hours to crack through brute force, while a 10-character password with upper & lowercase letters plus numbers could take up to 9 years! Proper use of all character types and increasing length to 14+ characters pushes estimates up to trillions of centuries to crack.
